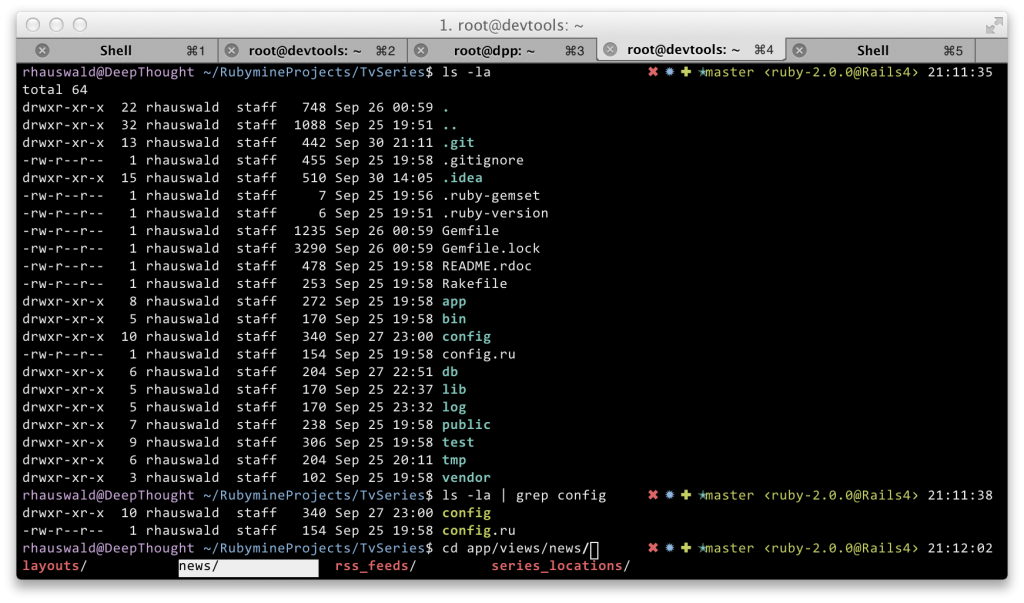
I recently moved from bash running in default terminal to zsh powered using oh-my-zsh running in iTerm2 on my development OS X and I won’t go back soon. Beautiful colors, wonderful custom prompts for the left and the right side of the screen as well as an awesome tab completion for nearly all the tools you need (git, rvm, git-flow, brew, bundler, rails, …). Have a look at the screen shot and in case you like it:
- The project website of oh-my-zsh: https://github.com/robbyrussell/oh-my-zsh
- A nice presentation of it: http://railscasts.com/episodes/308-oh-my-zsh
- A good how to install the current version of zsh and power it up using oh-my-zsh: http://ricochen.wordpress.com/2012/09/30/mac-os-x-lion-zsh-installation-with-brew-guide
- iTerm2: http://www.iterm2.com


Recent Comments